The cybersecurity landscape has undergone a fundamental and irreversible transformation in recent years. This shift is driven by the widespread adoption of artificial intelligence (AI) and large language models (LLMs) by cybercriminal groups and advanced persistent threat (APT) actors. Traditional defence paradigms, relying on manual human response and predefined, static signatures, are proving glaringly inadequate. When facing threats operating at so-called machine speed, a classic antivirus is merely an illusion of security. That is precisely why professional operating system hardening has become an absolute priority for every server administrator and network engineer. In an era where AI-based attacks are seeing an 89% year-on-year increase, proper server configuration, implemented Zero Trust architecture, and cutting-edge technologies like eBPF constitute the first and most crucial line of defence.
The Evolution of Threat Asymmetry and Machine-Speed Attacks
The average time attackers need to breach defences and begin lateral movement across a network (breakout time) has dropped to an unprecedented 2 minutes and 7 seconds. Worse still, according to global analyses (including a CrowdStrike report), in extreme cases of e-crime, this time has been compressed to a mere 27 seconds. The ability of artificial intelligence agents to autonomously plan, test, and execute multi-stage hacking operations within fractions of a minute drastically reduces the time window for an effective response from defenders.
An analytical report by Booz Allen Hamilton exposes a brutal reality: cybersecurity is entering a phase where malicious algorithms completely eliminate the time between the initial intrusion and the ultimate impact on the system. Unfortunately, most traditional defence architectures still operate based on human timeframes – incident analysis measured in hours, remediation in days, and patch deployment in weeks. Modern malware utilises automated reconnaissance to breach defences almost in real-time. With an estimated 2,200 cyberattacks occurring daily on a global scale, organisations are forced to entirely redefine their approach to security, where system hardening ceases to be a set of optional “best practices” and becomes a condition for survival.
The Maturation of Threats: From Phishing to Autonomous Agents
Although technology portal headlines often scare readers with fully autonomous malware, the reality is based on a gradual evolution. The AI Malware Maturity Model (AIM3) allows us to categorise the use of AI in attacks into specific levels:
- Level 1 (Experimenting): Attackers, researchers, and academia are creating prototypes, toy examples, and PoCs that leverage GenAI using rudimentary methods. At this stage, individuals are merely exploring the possibilities of GenAI and LLMs for malicious applications versus operationalising them in a serious manner.
- Level 2 (Adopting): Threat actors incorporate GenAI into familiar workflows such as authoring phishing emails, researching targets, and developing code. While the core operational tasks remain conventional, there is an emphasis on automating and supporting low-order tasks without reinventing traditional tradecraft.
- Level 3 (Optimising): Attackers are beginning to incorporate AI into their attack chains by leveraging GenAI on-host or via APIs to perform introspection, generate commands, and adapt code in near real-time. This is a shift in focus from bespoke GenAI use to treating GenAI as an integrated part of the attack chain.
- Level 4 (Transforming): AI-native offensive frameworks emerge at this level, combining multi-step planning and tool use with a Human-in-the-Loop (HITL) approach. These are the early, purposeful attempts at AI-first threat operations, utilising agentic patterns rather than bolting GenAI onto legacy playbooks.
- Level 5 (Scaling): Threat actors are building agentic systems to manage campaigns end-to-end with no human oversight. Automated decision-making is implemented at scale for the planning, execution, and persistence stages of operations. This level of sophistication represents the upper bound of GenAI capabilities that current experimentation is moving toward.
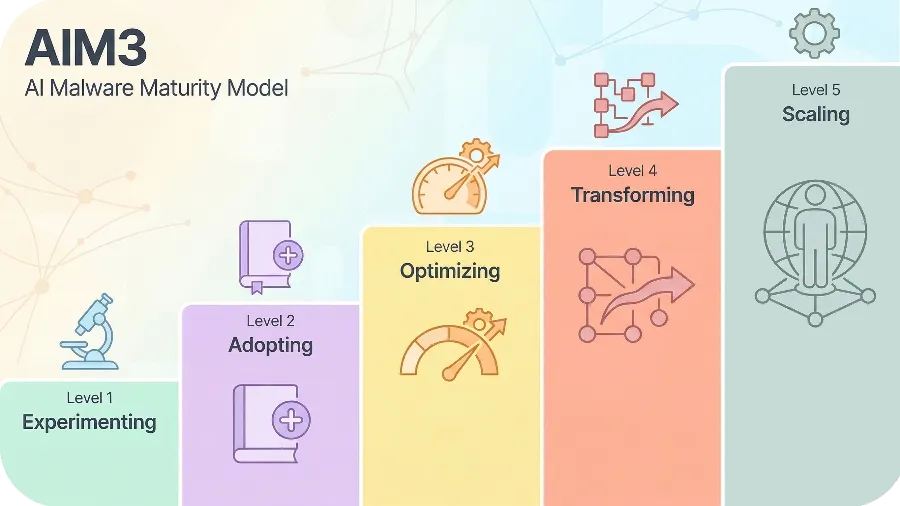
Currently, most real-world incidents sit at the early levels (1-3), where artificial intelligence acts as a force multiplier for existing hacking tools, drastically lowering the barrier to entry for cybercriminals with lesser technical skills.
Phishing remains the dominant vector of compromise, having evolved in a terrifying manner. Studies from 2025 show that nearly 82.6% of analysed phishing messages were generated using content created by artificial intelligence (tools such as FraudGPT or WormGPT). This allows for the generation of grammatically flawless and highly contextual emails, as well as the voice cloning of executives, which drastically facilitates the theft of initial credentials.
The Anatomy of LLM-Driven Malware
Today’s system hardening must account for the fact that malicious code no longer possesses a fixed, predictable form. The evolution of malware has entered a fully operational phase, where the programme’s behaviour is dynamically modified mid-execution.
An excellent example of a Level 3 (Optimising) threat is the PROMPTFLUX malware, acting as a VBScript-based dropper. It connects to the API of language models and instructs the model to regularly and entirely rewrite its own source code. The result is absolute polymorphism, neutralising detection mechanisms relying on static file signatures. The PROMPTSTEAL tool (often attributed to groups like the Russian APT28) operates similarly, using an API to generate native Windows commands in real-time, avoiding the hardcoding of malicious commands within its executable file.
In the Linux and cloud infrastructure world, we observe the activity of code like QUIETVAULT, which analyses pre-installed AI console tools on the infected machine to search for specific credentials (e.g., GitHub tokens or NPM certificates), facilitating devastating attacks on the software supply chain. Meanwhile, ransomware systems, such as the MalTerminal infrastructure, can dynamically modify encryption routines while an attack is underway. Faced with such threats, AI-based attacks easily bypass static firewalls, demanding a new philosophy of protection from us.
Foundations of Defence: From Hardware to Zero Trust
Conventional methods, where system hardening relied solely on software (e.g., DEP or basic ASLR), have exhausted their potential. Malicious autonomous AI agents, utilised for advanced fuzzing at processor speeds, rapidly locate Use-After-Free (UAF) or Out-Of-Bounds (OOB) vulnerabilities.
To halt this process, the software layer must be integrated with the physical security of silicon chips (Hardware-Assisted Security):
- Control-flow Enforcement Technology (CET): In Intel and AMD processors, this implements a “Shadow Stack,” neutralising ROP and JOP attacks that attempt to hijack the processor’s control flow.
- Pointer Authentication Codes (PAC): In ARM architecture, pointers use a fraction of the available bits for addressing, whilst the remainder is cryptographically signed by hardware keys, preventing the injection of non-native code.
- Memory Tagging Extension (MTE): A technology that “tags” memory blocks. An attempt by a malicious algorithm to exploit freed memory results in the silicon chip immediately terminating the task.
Zero Trust Architecture as the System’s Core
Even the best processor will not save an environment if, at the network and authentication level, we still trust old paradigms. Zero Trust architecture (ZTA) eliminates assumed trust, treating every access request as a potential threat. In a systemic sense, this means basing authentication processes on a continuous cycle of validation and real-time telemetry analysis.
Key pillars include the Principle of Least Privilege, implemented via Just-In-Time (JIT) and Just-Enough-Access (JEA) models. Zero Trust architecture also requires rigorous micro-segmentation, limiting the blast radius. If the QUIETVAULT agent compromises a container on a server, hard isolation rules will prevent it from moving laterally to the database. The “Assume Breach” philosophy is what makes Zero Trust architecture the most effective barrier when defensive algorithms lose the initial clash.
Environment Specifics: How to Effectively Implement System Hardening?
The process of securing infrastructure differs diametrically depending on the operating ecosystem, yet the goal remains the same – to deny malicious artificial intelligence room to manoeuvre.
The Linux Environment and the Power of eBPF
For the community gathered around the CreativeArt portal, Linux is the absolute centre of global digital infrastructure. The Linux kernel, due to its ubiquity, is a dominant target for the exploration of zero-day vectors involving artificial intelligence. System hardening in this environment relies on implementing mechanisms developed by the Kernel Self-Protection Project (KSPP), such as advanced KASLR.
The modern trust model in Linux, in turn, relies on Mandatory Access Control (MAC) extensions – platforms such as SELinux or AppArmor. Operating a MAC mechanism in “Enforcing” mode definitively limits which network resources and libraries a given process can open, hiding the base system from the gaze of mapping software steered by neural networks.

However, the true revolution in repelling malicious AI attacks is eBPF (extended Berkeley Packet Filter) and the LSM BPF system. Traditional kernel observation methods (LKM) carried a huge risk of kernel panic errors and gave potential intruders far too much access to the kernel. The eBPF solution is a universal framework allowing the compilation of specific fragments of programmatic logic within a secure virtual sandbox directly embedded in the kernel space. Thanks to eBPF, administrators gain “x-ray vision” into the nature of events with microsecond latency. This allows asynchronous tracking of every suspicious system call (syscall) generated by mutated malware, providing telemetry without which today’s system hardening would be doomed to fail. An alternative for critical-risk environments is the concept of “Immutable Infrastructure” (e.g., Talos Linux), where the file system operates in read-only mode from boot, physically blocking the injection of harmful routines.
Windows 11 and macOS in Corporations
Microsoft’s ecosystem is the main battlefield on endpoint devices. Here, system hardening is based on enabling Virtualisation-Based Security (VBS) features and the Hypervisor-Protected Code Integrity (HVCI) mechanism. They create a highly secured memory region separated from the kernel, eliminating the possibility of critical structure modification by rootkits. In an era where AI-based attacks focus on credential dumping, it is essential to enable Microsoft Defender Credential Guard, which isolates NTLM processes and Kerberos tickets from the sight of intruders.
For users of Apple hardware, the new “Apple Intelligence” architecture integrates protection mechanisms at an unprecedented level. Mandatory app notarisation, the hardware Secure Enclave, and processing AI logic based on Private Cloud Compute (PCC) separate modelling processes from untrusted networks, protecting corporate intellectual property from theft.

Does Wazuh Still Make Sense Against AI?
Many CreativeArt readers involved in administration ask themselves a key question: do free, open-source SIEM/XDR systems like Wazuh still have a raison d’être when cybercriminals use such advanced algorithms?
The answer is: yes, but Wazuh’s role must evolve. Classic Wazuh relies on static detection rules (decoders and rules based on regular expression signatures). In a clash with polymorphic malicious code (like the aforementioned PROMPTFLUX), which lacks a fixed structure, a static rule might prove “blind.” However, system hardening using the Wazuh platform remains a powerful foundation if properly integrated.
Firstly, Wazuh is an excellent log aggregator and Central Nervous System. When we enable advanced osquery integration and direct telemetry from eBPF modules for Wazuh agents, we gain profound behavioural insight into the Linux environment.
Secondly, the Active Response module built into Wazuh can be triggered based on atypical behaviour. Although Wazuh itself does not possess a native, top-tier machine learning engine for independent analysis, it can be easily integrated (via APIs and webhooks) with external AI assistants or behavioural analysis models. Wazuh then becomes the “hands” that immediately block an IP, close ports, or isolate a container using bash/python scripts mere fractions of a second after the integrated detection engine identifies an anomaly. Therefore, Zero Trust architecture relies heavily on continuous access to data, and few open-source tools collect it as efficiently and reliably on server systems as Wazuh.
Behavioural AI Detection: Fighting the Machine with a Machine
Proper system hardening at the OS level, an implemented Zero Trust architecture, and robust hardware create the foundation. However, classic defence can no longer stop LotL (Living off the Land) techniques, where malicious AI algorithms masquerade as trusted administrator tools. Therefore, it becomes essential to implement Endpoint Detection and Response (EDR) systems based strictly on behavioural detection principles.
Behavioural AI assesses operational intent and analyses the complexity of event chains. If a standard Word file suddenly begins using an unknown network pipe to modify the registry at 3 AM (or calls unusual services in the Linux user space), the behavioural model flags this as a critical deviation, asynchronously terminating the malicious thread without waiting for manual operator intervention. This is necessary because burnout and cyber fatigue amongst engineers (alert overload) constitute one of the biggest threats in the IT industry today. Tools from the Agentic Security Operations space help process hundreds of signals, consigning traditional antiviruses to the history books.
Summary
In times when AI-based attacks breach defences in under a minute, operating system hardening cannot be treated as a one-off audit. It is a continuous process encompassing hardware, rigorous permission policies built into the system kernel (like eBPF or HVCI), and advanced log analysis. A properly implemented Zero Trust architecture is no longer just a buzzword, but a real technical requirement. Despite the evolution of threats, powerful monitoring tools like Wazuh, coupled with next-generation telemetry and automated response scripts, still form a crucial cohesive element for the security of any server room. If your organisation still relies exclusively on static signatures, it means you have lost the race before it truly began.





Leave a Reply